Though less messy than changing them, manufacturing disposable diapers is certainly more complicated, especially when the machines that make them need to combine control and safety functions.
Many of these 120-ft-long machines are made by Curt G. Joa of Sheboygan Falls, Wis., which builds its devices by assembling them from a dozen or more 10-ft machine sections (Figure 1). The firm’s users produce diapers, bandages and absorbent pads, and so Curt G. Joa reports its applications require a lot of additional customization.
Jim Montague is the executive editor for Control. Email him at [email protected].
“We’re doing control and safety on the same wire, even though we don’t see a lot of other people doing it,” says Kevin Zeinemann, PE, Joa’s electrical engineering manager. “This is because one of our diaper manufacturers that previously bought a hardwired machine wanted to add safety PLCs. Over the years, we had experience with proprietary lockdown safety systems, and they had a lot of initial expenses and many added costs to customize. These earlier machines had to be updated constantly, and it was a real hornet’s nest.”
When Joa sought a safety PLC, it ran across Rockwell Automation’s GuardLogix PLC with safety functions, which is supported by RSLogix 5000 software and runs via DeviceNet and EtherNet/IP network protocols.
“The user was prepared to pay for a safety PLC, and we were sold on GuardLogix because we’d already standardized on its core logic, so it was easier for us to implement,” says Zeinemann. “We did two machines for this customer, and, though there weren’t initial total savings on equipment, the cost of these improvements was much less than what it would have been otherwise because of savings on labor, common hardware and software and troubleshooting efforts. The individual control modules in our machine sections were easier to build, ship and plug and play, and so we had much easier modularity and less downtime. And, even though our new machines are more complex and have new capabilities, our installation and checkout time is the same as before. We’re just looking to build our machines faster, and this helps us do it, even though we still have a lot of customization.”
Flirting with Fieldbus? Seek Standards, Too
It’s these potentially huge savings in network hardware, labor and time that attract users, integrators and developers to digital networks, fieldbuses and wireless in the first place. However, despite all the gains that digital controls networks have made in recent years, most potential users still stop short when safety gets mixed into the equation. Because they don’t want to injure colleagues, damage equipment or halt costly operations, users and integrators often default to traditional, hardwired networks when safety is needed or required.
To gain some reassurance, most users also rely on industry-defined standards for networks and other components used in discrete and process applications. These standards include rules and best practices for networks that vary widely in their specificity and requirements. For instance, mostly for discrete applications, the two most recent National Fire Protection Assn. updates to its NFPA-79 standard in 2003 and 2007 allow use of safety-certified PLCs for safety and control communications on the same physical network. As a result, many suppliers developed and launched safety PLCs and other devices able to combine safety and control and have sought safety certifications for them from TÜV Rheinland or other independent, safety-testing organizations.
“NFPA-79 is the common standard for control system development in North America, and all machine specification includes it and other ANSI standards and UL requirements as needed,” says Kelly Schachenman, Rockwell’s safety business marketing manager. “The NFPA-79 update in 2003 allows solid-state safety PLCs without an air gap in their output string as long as they’re properly safety-certified and part of an overall risk-assessment program.”
Likewise, mostly for the process side, the International Electrotechnical Commission’s 61508 and 61511 standards cover safety requirements for process applications. IEC 61511 is designated by the International Society of Automation as ISA S84.00.01-2004.
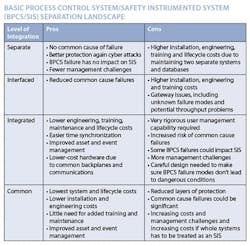
“IEC 61508 calls for separate control and safety systems, but it doesn’t prescribe how the user should do it,” says Luis Duran, safety and critical control marketing director for Invensys Process Systems. “When you try to mix safety and control on the same box, there are provisions you must make to be sure your application is safe, and this is why a risk assessment is necessary to determine what level of separation is needed and how to achieve it. Essentially, developers and users need to ensure that any issue affecting control on one layer won’t affect safety on another layer.”
Some Integrators are Skeptical
Despite the huge savings promised and standards that allow them, most end users and system integrators doubt that combining control and safety communications on one network can be completely safe.
“We see a lot more focus on safety in the automotive applications we work with, and the devices we work on that have DeviceNet and EtherNet/IP can do safety and control on one wire,” says Joe Mixon, a system integrator at LEC in Pearl, Miss. “However, I haven’t seen it done on any machines yet, and we still hardwire for safety. I think most folks are scared to do it because they feel combining control and safety is still too new and unproven, but it’s also because we don’t have enough hard and fast, prescriptive rules about how to safely build and run applications. So much of safety is driven by litigation after the fact. As a result, we just have to do what we think is right and hope we don’t get caught with our pants down.”
Jason Perry, project engineer at control system integrator Matrix Technologies in Maumee, Ohio, agrees that users are especially fearful about combining control and safety networking because they have to change their whole philosophy from hardwiring to digital and do it in a place where they need high reliability for critical applications. “Engineers also worry that their technicians could be overwhelmed if something goes wrong, and so they decide to let someone else try it first,” he adds.
Redundancy on the Black Channel
The original shift from hardwiring to digital networks meant migrating from point-to-point, usually 4-20 mA cabling in process applications, between every field device and the centralized controls to one twisted-pair cable that links and transmits data from all the devices along it in various topologies. The push to integrate safety is very similar, but has been stymied because users and integrators are reluctant to alter safety systems.
However, just as Ethernet’s developers used hardware gateways for software-based intelligent switching and addressing to provide determinism, efforts to integrate safety and control likewise employ methods that identify, address and schedule data for reliable transmissions and delivery. Basically, this recreates in software the hardwired redundancy capabilities on which traditional safety systems are founded.
Perhaps the best known of these methods is the dramatic-sounding Black Channel. “This simply involves adding security and encryption functions to regular addressing methods and network hardware to help check safety messages, make sure they get to their intended destinations, verify that the recipient understood the message and check that appropriate actions were performed,” explains Duran.
For example, Zeinemann reports that some of the safety functions in Joa’s diaper machine are maintained and protected by GuardMaster interlocking guard switches wired into EtherNet/IP safety I/O modules. “Users can access and read safety information in their control routine, but they can’t turn any safety outputs on or off as part of their normal tasks,” explains Zeinemann. “The safety aspect is very specific, only allows authorized changes and then locks them down with a password. In fact, this method is a lot safer than someone possibly adding an unauthorized jumper to a hardwired system.”
Discrete Leads Integration
It’s no accident that more discrete applications are further along in integrating control and safety. It’s mainly because powering down a production line is a lot simpler than the often complex procedures needed to stop many continuous process applications or get them to a safe state.
For example, to become a Tier 1 supplier of auto bodies to Chrysler, Kuka Flexible Production Systems recently updated the robots and related systems at its Kuka Toledo Production Operations (KTPO) assembly plant, which makes bodies and chasses for Jeep JK and Wrangler vehicles (Figure 2). In short, Kuka’s engineers wanted to reduce traditional hardwiring to its safety equipment and in its large control cabinets, thereby increasing application flexibility, cutting troubleshooting costs and making its machines more affordable.
As a result, one of Kuka’s engineers, Rod Brown, reports his company moved from safety relays to safety PLCs and also implemented safety and control with Siemens E&A’s Profibus-based processor via its Profisafe protocol. By combining safety and standard I/O, along with a common programming method, Kuka’s engineers say they achieved an 85% percent reduction in relays, local I/O, terminal blocks and cable connections, slashing labor costs.
“We built the system in no time, and commissioning was surprisingly easy,” adds Brown. “This approach saved us tens of thousands of dollars on the first installation alone.”
Process Catching Up
Meanwhile, on the process automation side, Kristian Olsson, manager of ABB’s Safety Center of Excellence, reports one early pioneer of integrating control and safety is Dow Chemical in Midland, Mich., which analyzed how to implement process and safety applications in the same controller. In a presentation at ISA Expo 2007, Dow’s Ron Johnson said his company introduced layers of protection analysis (LOPA) in 2000 as the primary way to determine the need for and the integrity level of safety instrumented functions (SIFs), and Dow also began to adopt the principles and methodology of industry-standard IEC 61511/ISA-84.00.01-2004. Dow’s teams also realized that many SIF components to reduce failure probabilities or reduce spurious plant trips were redundant. This spawned the concept of sharing redundancy between various LOPA layers.
“If done properly, sharing can reduce a safety system’s failure probability because the SIS is still functional even after one sensor fails, while at the same time plant upsets due to false trips are reduced because control still is maintained, even if one sensor fails,” explains Johnson. “The shared equipment must be designed appropriately, so when it’s combined with the remaining protective layers, the unwanted event is adequately managed.”
More recently, ABB worked with Dow Chemical to update and launch its new 800xA SIL 3-rated safety system. Olsson says 800xA can host safety and critical-control applications in the same controller, while providing logical separation of control and safety functions. This same-yet-separate architecture is designed to protect personnel, the plant and the environment, while proving significant operating efficiencies. ABB worked with Dow to develop and launch 800xA after Dow had gained all the benefits it could from its proprietary system.
FF-SIF Integrates Safety at Shell
Probably the largest, most ambitious effort to integrate control and safety in process applications is Foundation fieldbus safety instrumented function (FF-SIF) technology, demonstrated in May 2008 by the Fieldbus Foundation and a host of jointly cooperating end users and suppliers at Shell Global Solutions’ technology center in Amsterdam, the Netherlands.
In addition, three other end-user participants conducted simultaneous FF-SIF demonstrations of their own. They included Saudi Aramco in Dhahran, Saudi Arabia; BP in Gelsenkirchen, Germany; and Chevron in Houston. These included systems and products from all major process automation suppliers.
To run the Amsterdam demonstration, FF-SIF working groups consisting of nearly 30 process industry users and vendors built a fieldbus-based, safety-shutdown system rig at Shell’s laboratory (Figure 3). It included logic solvers, safety devices and SIFs. The demonstration was designed to evaluate FF-enabled safety valves with partial-stroke testing (PST) capability, as well as pressure and temperature devices. System integration capabilities with asset management and basic process control system (BPCS) platforms also were evaluated.
While conducting the live FF-SIF demo, Shell’s Audun Gjerde demonstrated high- and low-level trips, partial-stroke valve testing and a partial-stroke test interrupted by the emergency shutdown (ESD) system. This showed that, even in the middle of a partial-stroke test, the ESD could take over and shut down the system successfully during an abnormal situation. Two-out-of-three (2oo3) voting was shown using fieldbus SIF devices. The system also reacted successfully to a temperature-probe loss, a measurement-validation alarm and a diagnostic alarm generated from a dry probe on a level device.
Gjerde says the demo project sought to have a logic solver fully operable with all available SIF devices, to integrate an asset-management system with the SIF devices and to integrate SIF partial-stroke testing/valve-stroke testing within a safety system infrastructure. “By implementing FF-SIF, Shell expects enhanced diagnostics through a fully integrated asset management system,” explains Gjerde. “We also anticipate less testing of final elements thanks to smart testing and diagnostics, as well as online testing and partial-stroke testing. This will result in early detection of dangerous device failures and fewer spurious trips. The added SIF diagnostics will help engineers and maintenance personnel increase the integrity of the plant by ensuring maintenance is performed where and when it is needed. With smart online testing and diagnostics, we’ll be able to run for longer periods of time without shutting down the plant for testing. We’ll also save on the cost of adding a second or third device in many cases.” The system included products from a variety of vendors. In addition, FF-SIF meets IEC 61508 functional safety requirements, up to and including SIL 3. End users can build systems to the IEC 61511 standard covering SIF functional safety in the process industries. Major suppliers are expected to begin offering FF-SIF products in 2011.
More, Closer Integration Coming
In the future, control and safety networks will only become more integrated. Zeinemann reports that Curt G. Joa also plans to implement CIP Safety and CIP Motion capabilities in its machines to give them safe motion functions when they become available in RA drives. “The true advantage of doing control and safety on the same wire is that the hardware is all the same,” explains Zeinemann. “The drives, modules and I/O points already are tested and work together, so all we need is one more building block to make safety happen.”
Zeinemann adds that machine builders don’t have to fear combining control and safety, as long as they use certified and approved equipment properly. “Just understand what’s under the hood of your machine, and then trust that you can use approved safety tools for it, ” he says. “The modularity you’ll achieve will make everything easier.”
About the Author
Jim Montague
Executive Editor, Control
Jim Montague is executive editor of Control. He can be contacted at [email protected].