Device-level protection for CRA-ready industrial networks
Key Highlights
- The EU Cyber Resilience Act (CRA) mandates strict cybersecurity compliance by December 2027 for any manufacturer selling digital products within the region, regardless of their global location.
- Achieving robust operational technology (OT) security increasingly relies on adapting proven IT technologies, such as TLS and PKI, to protect industrial connectivity without sacrificing system availability.
- CIP Security for EtherNet/IP provides a scalable, standardized path for industrial suppliers to meet modern regulatory requirements by embedding device-level protection into both new and existing automation systems.
Some cyber assaults are merely inconveniences in the consumer realm, and others are high-profile banking or data breach incidents, but there are also countless events involving digital products throughout the manufacturing sector and infrastructure operations. For years, industrial suppliers have progressively improved the cybersecurity aspects of operational technology (OT) hardware, software and connectivity products. This has been prompted and directed in part by end users and by various standards and guidelines such as ISA/IEC 62443 developed to manage and reduce cybersecurity risks. Most recently and prominently, the European Union (EU) has created the Cyber Resilience Act (CRA) to strengthen all types of digital system cybersecurity, in products as different as household robotic vacuums and industrial factory robotic arms.
The increasing availability of compute power, even in the smallest and most remote of devices, and the proliferation of digitalization projects for gathering and analyzing data, mean that connectivity among these devices and systems is a fundamental need for any solution. Widespread connectivity creates even greater cybersecurity exposure and risks. Fortunately, in many cases cybersecurity solutions developed and proven throughout information technology (IT) implementations are forming the basis for achieving robust OT cybersecurity.
Guidelines, regulations and compliance
Cybersecurity guidelines and regulations are not new. The U.S. National Institute of Standards and Technology (NIST) Cybersecurity Framework (CSF) is a set of guidelines developed in 2014, acting as a tool for achieving cybersecurity in critical infrastructure sectors. The EU Network and Information Systems (NIS) Directive, introduced in 2016 and then expanded as NIS 2 in 2022 with stronger enforcements and broader sector coverage, were established to regulate critical sectors in member states.
However, the CRA is even more comprehensive in several ways, and compliance is required by December 11, 2027, with significant penalties for non-compliance. It applies to the manufacturers and suppliers of a broad range of products with digital components and connectivity—basically anything that processes data—and therefore pertains to not only consumer devices, but also to many products used in all types of OT applications. While this is an EU regulation, it impacts any supplier intending to sell into that region, so it is garnering worldwide attention. However, the CRA is a legal framework and not a detailed technical implementation guide, although work is ongoing to enhance the CRA with clear technical requirements based on product type. It mandates secure-by-design principles, vulnerability management processes, robust documentation practices and a rigorous product development lifecycle.
Creating cybersecure products comes at a cost: more processing power is needed, design and management efforts are intensified, and performance can be reduced. For most suppliers and implementors, the approach for creating CRA-compliant products and designs will rely on leveraging key technologies already proven throughout other commercial and IT industries for the most critical sectors, such as banking.
ODVA was founded in 1995 as a standards development organization (SDO), whose members are global suppliers for industrial automation applications. A key ODVA technology is the Common Industrial Protocol (CIP), which is an industrial communications protocol deployable on various media. CIP, in the form of EtherNet/IP, DeviceNet, and other protocols, is widely used throughout industry to provide an object-oriented approach for messaging and data presentation. Just as ODVA has progressed the CIP standard to take advantage of newer media, CIP cybersecurity aspects have also been enhanced via the CIP Security network extension for EtherNet/IP.
Cybersecurity for industry
For digital communications purposes, the confidentiality, integrity and availability (CIA) triad outlines three objectives which must be considered. In addition, establishing the authenticity of users, applications and devices is crucial; basically, ensuring that proper and expected elements are interacting with each other without any undesired outside influence.
Banking, purchases, email and other networked and internet-connected IT applications require effective confidentiality. This is why internet browsing, which was once completely “open,” has been enhanced over the years by the addition of Transport Layer Security (TLS) and public key infrastructure (PKI) to issue, validate and manage the certificates that enable authentication and encrypted communication (Figure 1). The result is that almost all web browsing is performed with the familiar encrypted and secure “https://” address prefix to prevent eavesdropping and tampering. This progression has been almost completely transparent for end users.
The CIA balance for most OT applications is different from that for IT. For OT, data availability and integrity have been paramount to support always-on performance, while confidentiality and even authenticity have been generally less important. Older OT networks, particularly those which were highly localized with relatively few nodes, did not present much of a physical target for cybersecurity. Moving forward, especially as wired and wireless Ethernet have become preferred networking media, OT products’ authenticity and integrity and sometimes confidentiality, when conditions warrant, must be improved to achieve CRA compliance, but availability must not be sacrificed (Figure 2).
Implementing CIP Security for EtherNet/IP
In the context of OT industrial communications, ODVA has progressively developed the CIP standard to meet the evolving needs of industry. DeviceNet uses CIP over the proven controller area network (CAN) media layer at a selection of speeds and distances to interconnect devices for deterministic data exchange. ODVA conformance testing and device profiles ensure consistency among products. DeviceNet has been a foundational digital communications protocol for countless industrial installations, including programmable logic controllers (PLCs), input/output (I/O) modules and valve manifolds, variable frequency drives (VFDs).
As Ethernet media became physically practical for industrial installations, ODVA adapted the proven and familiar CIP standard to create the EtherNet/IP protocol, with enhanced bandwidth and node counts as compared to DeviceNet. For users with more demanding requirements, CIP has been extended with services for security, safety, motion control, time synchronization and energy usage. These extensions are carefully architected to add the new functionality, including suitable determinism for a wide range of industrial applications, while remaining compatible to avoid “breaking” existing applications.
Get your subscription to Control Design’s daily newsletter.
Following the same evolutionary pattern of IT-based security, the CIP Security extension has added a TLS layer and PKI handling to EtherNet/IP (Figure 3). Using CIP Security, designers can incorporate more secure EtherNet/IP communications with devices when and where it is needed, and devices can be offered with different profiles supporting varied security levels.
Because CIP Security for EtherNet/IP is built on proven, open, and well-established OT and IT standards, users preserve their investments in training and knowledge, and they will realize a straightforward path to incorporate the new technologies. Security can be designed into new projects, or it can be added in the form of a top-level proxy device to protect existing underlying devices or systems that would not otherwise be upgraded.
Certainly, there is some additional work and complication involved with implementing secure communications, just as there was when moving from simple DeviceNet node numbers to the complexity of IP addresses introduced with EtherNet/IP. System integrators and OT network engineers will need to understand, install and manage a PKI host server with appropriate CIP routing at the site and create authentication certificates. Good physical and logical network segmentation, which has always been important, is now even more essential from the factory floor up to the enterprise.
Multivendor support and alignment are central to ensuring security integrity. Procedures, testing and documentation are necessary to validate the design because an apparently normal-working system might still be vulnerable from a cybersecurity standpoint.
Building cybersecurity on a proven foundation
Considering all of this, CIP Security for EtherNet/IP offers tremendous value for designers tasked with fulfilling CRA cybersecurity requirements for new products and systems and for retrofits, as well. The entire stack has been built upon existing and proven technologies and standards, continually enhanced since around 2020. There is a large installed base of EtherNet/IP products, along with significant end-user awareness of and expertise with the TLS and PKI technologies used throughout IT. CIP Security makes PKI and other cybersecurity technologies as easy as possible to deploy in an OT setting.
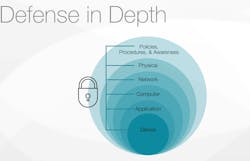
CIP Security offers device-level protection for critical applications where a cyberattack could result in significant economic, environmental or physical harm. Used as a part of a defense-in-depth approach, along with other security methods including appropriate network architectures and segmentation, firewalls, deep packet inspection, zones and conduits, updated device patching, employee training and physical access restrictions, CIP Security can help prevent bad actors from disrupting business operations (Figure 4). Device-level security is the last mile of protection for industrial automation motion devices such as valves, drives and grippers.
The Industrial Security Harmonization Group (ISHG) is one of many collaborative activities in which ODVA is engaged to ensure that end users across industries benefit from a consistent application of the technologies they utilize. As a part of the ISHG, ODVA joins other industrial automation standards development organizations including FieldComm Group, OPC Foundation and PI to work to harmonize cybersecurity strategies and concepts, so that end users do not face unnecessary complexity when using security concepts in their automation systems. Providing end users with common education resources along with unique defense-in-depth network options, such as CIP Security, enables greater solution adoption and ultimately more secure facilities.
Industrial automation applications are quite diverse and customized, ranging from small machines to large factory installations. More than ever, there is a demand to interconnect increasingly intelligent devices and gather massive amounts of data. To provide acceptable cybersecurity, industrial automation equipment and system integrators need connectivity devices and technologies that are robust and flexible and fulfill CRA requirements, preferably using technologies they have become familiar with over the years. CIP Security for EtherNet/IP meets these needs in a scalable and accessible way, helping organizations to create cybersecure products.
About the Author
Joakim Wiberg
ODVA
Joakim Wiberg is the director of technology at ODVA. He has gained extensive experience over almost three decades of technology and product development for industrial network systems, with about half of that duration associated with aspects of cybersecurity. Wiberg holds a bachelor of science degree in electrical engineering and a master of science degree in computer systems engineering from Halmstad University, Sweden, and also holds two patents. Contact him at [email protected].